At Camilion we take security seriously, which is why we engage in
all reasonable precautions to ensure the software you get is the software we
design.
Amongst other things we sign our code digitally and, the topic
of this post, we make sure that your end users are talking to our servers and
not to something else.
Here we will explain to you how that works and how, in certain environments,
that can lead to issues.
Should you have these issues, read the section
What to do if I have a TLS-proxy?
User to Server Communication
Whenever you open our webpage, install our software or sign in to access your
trials or licenses, your device must contact our servers.
Given how the internet works, the data you send to us (e.g. your email to sign
in) and the data we send to you (e.g. our Sheeets for Autodesk®
Revit®) passes through countless devices outside of both your and our control.
Such devices can be routers, firewalls, proxies, etc.
Transport Layer Security (TLS)
Our goal is to ensure your Personal Information is safe, and to be be reasonably
sure that nothing strange is going on on the network.
To do this, the data in that travels through the network is encrypted using
Transport Layer Security (TLS), this ensures that,
for practical purposes, the connection looks like this:
______ Email __________
| Your | --------> | Camilion |
|Device| Program | Servers |
|______| <-------- |__________|
And that none of the devices that forward the information between you and us
are able to read or modify the information.
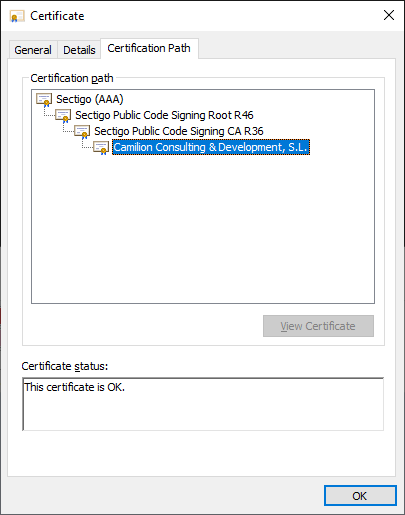
Chain of Trust
We introduced the concept of the Chain of Trust when we talked about
Code Signing Certificates, in this case it works very
similarly.
Your computer has pre-installed a set of Root Certification Authorities, that
sign / trust Intermediate Authorities, which in turn end up signing or trusting
end certificates like ours.
That is, a Chain of Trust can be built.
What are TLS proxies?
However in certain environments, so-called TLS proxies are used which install
custom Root Certification Authorities on your devices and intercept all
communications.
______ Email _______ Email?? __________
| Your | ----------> | TLS | ---------> | Camilion |
|Device| Program?? | Proxy | Program | Servers |
|______| <---------- |_______| <--------- |__________|
/
good? __/ ___ Can see/modify your data
evil? Can modify our software
Notice that this scenario breaks the warranties of privacy and integrity;
that is, we cannot be sure that your Personal Information is secure and we can
also not ensure that you are getting the software as we designed it.
Which is why our software detects TLS-proxies and refuses to work with them.
When are TLS proxies used?
There are many reasons, the most common one is to limit or filter what
users or employees can do on the network or with corporate equipment.
However, and it is not entirely uncommon, in some cases there is indeed a case
of Mensch in the middle attack which can be targeting you or your
company for many reasons including: phishing, ransomware, corporate espionage,
etc.
We call this Mensch in the middle attack, Mensch means “human” in German.
Traditionally “MITM” stands for “Man in the middle attack”.
What to do if I have a TLS-proxy?
Now that you know what a TLS-proxy is and why our software will refuse to work
in such a scenario, let’s look into what you should do next.
First, get in touch with your IT services, feel free to send them this link and
have them confirm that it is them who are running such a TLS-proxy; if it is not
the case, have them scan your equipment for malware.
Once that is cleared up, your IT services should get in touch with us so we can
figure out a way to have our software work for you.
There are basically two options:
- Preferred one: they add an exception to our servers, so the connection is direct between your devices and us. For this, IT will usually need the involved hostnames:
apps.camilion.euandcamilion.eu. - Last-resort: they send us the public parts of their custom Root Certificates and we add an exception.
Either way, the pros and cons are best discussed in a case-by-case basis with
your IT services.
Conclusion
As you can see, we are committed to keeping you and your data secure.
Sometimes there are policies that go against each other, but with the beauty of
collaboration we can make things work out.
Not many of you will run into these issues, and if you do, let’s find a
solution together.
For the rest of you, we hope you have learned some more and it helps you stay
safe on the internet!